Singapore Math Heuristics: Draw a Table, Make Suppositions and Use Before-After Concept

7 Ways Math Enrichment Boosts Your Child’s Math Success
Every parent wants their child to enjoy learning and succeed in math—and every child can do well in math. It just may happen at a different pace for each learner. The traditional classroom, with its fixed structure and broad focus, isn’t always able to meet every child’s unique learning needs. That’s where math enrichment can […]

Math Tuition vs. Math Enrichment: How to Choose the Best Math Program for Your Child
The world is evolving with advances in technology and artificial intelligence, reshaping the way we live, work, and learn. In this changing landscape, math education is no longer just about doing calculations quickly—machines can already do that. What’s becoming more important are skills like problem-solving, logical thinking, and the ability to adapt. As the demands […]
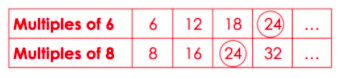
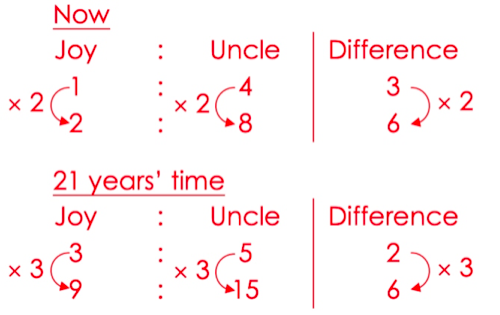
Singapore Math Heuristics: Solve Part of the Problem, Simplify the Problem and Work Backwards
Problem-solving in mathematics helps children develop reasoning and communication skills that are transferrable and important life skills. Reasoning is required on three levels when children solve word problems. First, they use reasoning to recognise what information is provided or missing. Then, they use reasoning to figure out what information they need to find. Finally, they […]

Singapore Math Heuristics: Make A Systematic List, Guess And Check, Restate The Problem In Another Way
The skills children pick up in math are indispensable; they can be applied to other academic subjects and to solve real-world problems in their daily lives and future work. The Singapore Math curriculum focuses on problem solving. Through problem solving, children develop thinking skills such as creative thinking and critical thinking. When children analyse math […]